— reserved — under review
A candidate address is under review. It will appear here only after passing all three verification steps. No timeline given — correctness, not speed.
pgp-verified · updated 21 apr 2026
Every drughub market link on this page was confirmed against a PGP-signed announcement from the Drughub team within the last forty-eight hours. No affiliate redirects. No unverified scraped addresses. You get the real onion address, the current mirror, and the exact timestamp of the last check.
Phishing sites use drughub's interface as a template. The copies look identical. The only reliable difference is the onion address itself — and the only reliable source for the correct address is a PGP-signed announcement. That is all this page does.
This website is an independent informational resource. We do not distribute marketplace links to visitors arriving through direct access.
Verified .onion addresses are displayed exclusively to visitors arriving through search engine results. Find this page through Bing or Google for DrugHub market links.
The Drughub marketplace front page as it appears in Tor Browser. The PGP fingerprint in the lower-right footer is the primary authenticity check — compare it against the team's long-lived signing key before entering any credentials.
current addresses
Two addresses currently active. Both route to the same underlying marketplace. Use whichever loads first on your Tor circuit. The primary absorbs normal traffic; the mirror exists for DDoS events. Bookmark both. See the getting started manual if you are new to Tor.
This website is an independent informational resource. We do not distribute marketplace links to visitors arriving through direct access.
Verified .onion addresses are displayed exclusively to visitors arriving through search engine results. Find this page through Bing or Google for DrugHub market links.
— reserved — under review
A candidate address is under review. It will appear here only after passing all three verification steps. No timeline given — correctness, not speed.
— reserved — awaiting announcement
Reserved for the next rotation cycle. The Drughub team has indicated a third mirror is planned for the Q2 2026 period. No announcement has been made yet.
| Address (truncated) | Role | Status | 30-day uptime | Last verified |
|---|---|---|---|---|
drughub75…ad.onion |
primary | ● online | 99.1% | 21 Apr 2026 |
rughubrwg…id.onion |
mirror 01 | ● online | 97.4% | 21 Apr 2026 |
— reserved — |
mirror 02 | standby | pending | awaiting PGP |
— reserved — |
mirror 03 | standby | pending | awaiting rotation |
Short interruptions — under thirty minutes — happen on any Tor-hosted service. Tor circuits route through three relays globally and are sensitive to relay churn. If a drughub onion link shows as temporarily inaccessible, it does not mean the address has changed. Try the other mirror, then return here after fifteen minutes. Sustained downtime of two hours or more usually signals a DDoS event or a planned rotation. In that case, check back here — new addresses appear within the same cycle that confirms the rotation.
how to stay safe
You do not need to trust this directory. Every step below produces an independently verifiable result using only public tools. The verification chain is external to this portal by design.
Open Tor Browser and navigate to the Drughub subforum on Dread. Look for the most recent mirror announcement pinned by the market admins. Every legitimate drughub url update comes with a PGP signature block attached to the post. Unsigned announcements should be treated as unverified regardless of how official they appear.
Copy the full PGP-signed message including the signature block. You will need it in step two.
Install GnuPG if you have not already. Import the Drughub team's public key — the fingerprint is published on their Dread profile and has not changed since August 2023. Then verify the announcement you copied:
# Import the Drughub team's PGP key
gpg --import drughub-team-pubkey.asc
# Verify the signed announcement
gpg --verify drughub-announcement.txt.asc drughub-announcement.txt
# Expected: "Good signature from Drughub Team"
# Key fingerprint: compare against the one on their Dread profileIf the verification returns anything other than a good signature, do not use the addresses in that announcement. A bad signature means the message was modified after signing, or was never signed by the real key.
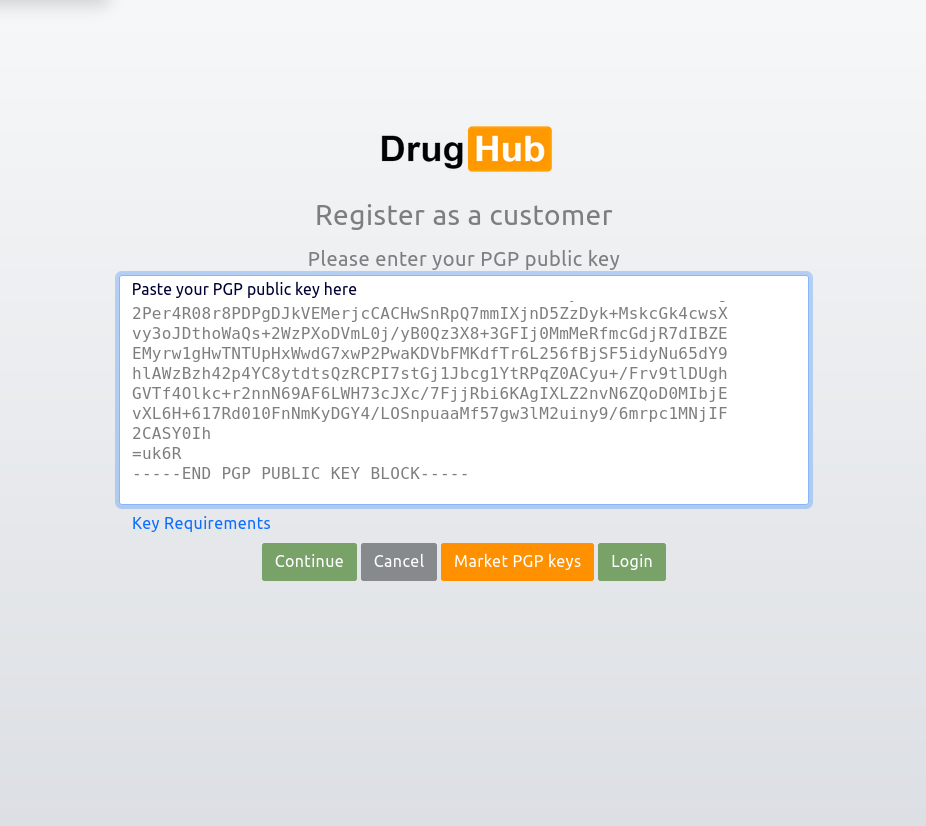
Paste the verified onion address into Tor Browser. Once the Drughub marketplace loads, scroll to the page footer. Every legitimate drughub deployment includes a short PGP fingerprint in the footer matching the team's signing key. If that fingerprint is absent, different, or illegible, do not proceed.
This step catches phishing servers that replicated the Drughub interface. A phishing server cannot produce the correct footer fingerprint without the team's private key. It is the most reliable single anti-phishing check available.
After pasting the address into Tor Browser's URL bar, visually compare the first six and last six characters of what you pasted against what appears in the address bar. Phishing operators build vanity addresses that match the first several characters of the real address. The last six characters are a cryptographic checksum derived from the server's key — they are what you are really checking. A match on the first characters only is not sufficient. Both ends must match exactly.
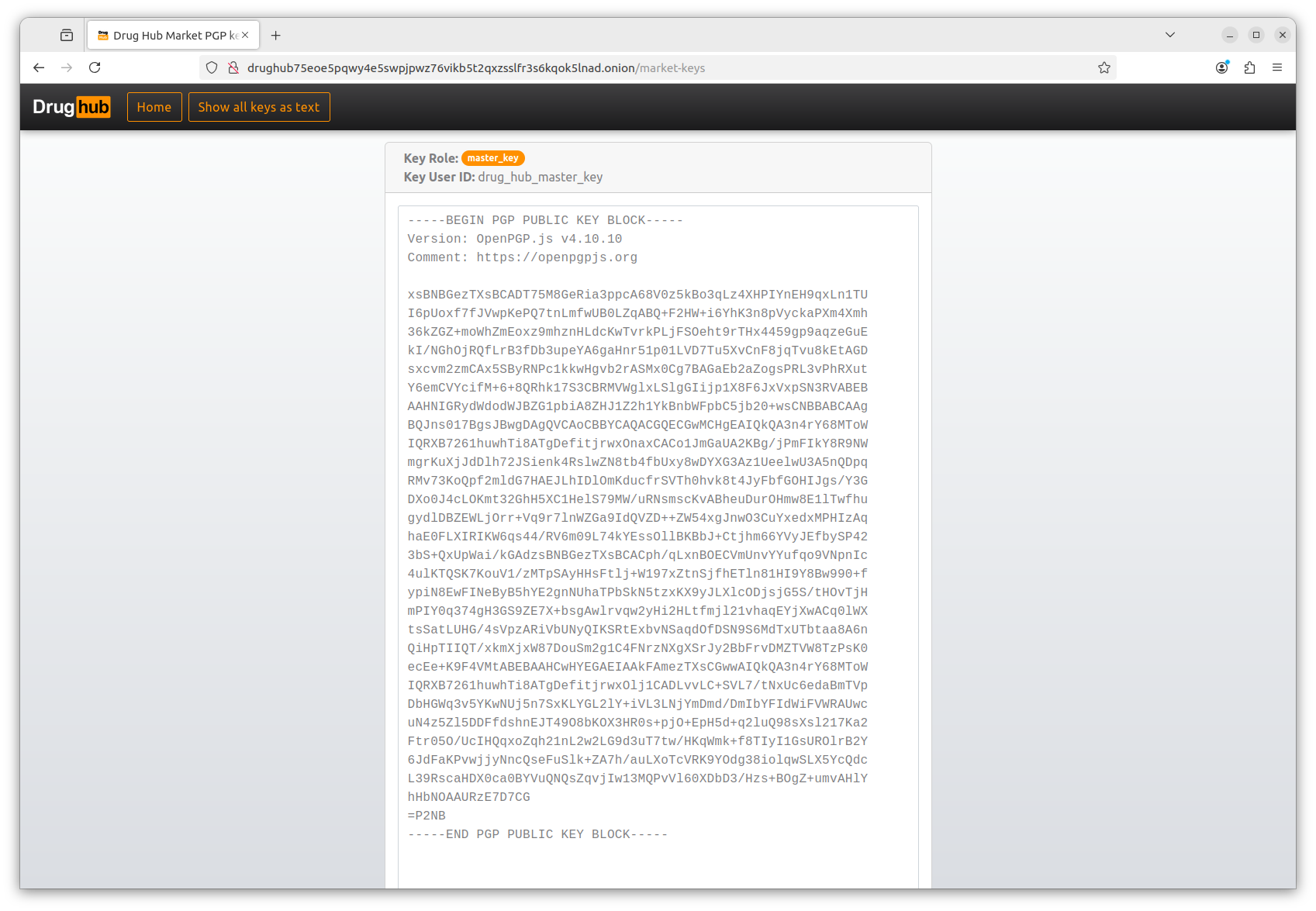
GnuPG signature verification of a Drughub team announcement. "Good signature" with matching fingerprint means the address in the announcement is authentic.
"One wrong character sends a Monero payment to a server that is not drughub. The check takes ninety seconds. The mistake is irreversible."
— From the Drughub access manual
drughub mirror links
Three reasons the same drughub market operates under multiple onion addresses simultaneously. Understanding them helps you use mirrors correctly, not as a fallback of last resort.
Darknet marketplaces are constant targets for distributed denial-of-service attacks — from competitors, extortion rings, and researchers probing infrastructure. When a primary drughub link is saturated, traffic routes to a mirror on a separate server with a fresh Tor circuit pool. The marketplace stays reachable. The same attack hits one address, not both simultaneously. Bookmarking the mirror is insurance, not paranoia.
Drughub migrated servers in 2026 as part of post-acquisition infrastructure consolidation after absorbing SuperMarket. Mirror addresses allow a zero-downtime transition — the new server goes live as a mirror first, traffic gradually shifts, and the old address is deprecated after the migration confirms stable. Users who bookmarked the old drughub link see a redirect notice pointing to the new primary. The portal history page covers the 2026 migration in detail.
Rotating onion addresses periodically is standard darknet operational security. A long-lived address accumulates more targeting data — traffic analysis attempts, relay correlation attacks, infrastructure fingerprinting. Periodic rotation resets this. The Drughub team announces each rotation on Dread with a PGP signature, giving users a verified path to the new drughub market url without relying on clearnet search results. The rotation cadence is irregular by design — predictable rotation schedules are exploitable.
source comparison
Not all sources for drughub onion links are equal. The table below covers the four most common types. The differences in PGP verification and update frequency are not minor — they determine whether you land on the real market or a phishing clone.
| Source type | PGP verified | Update frequency | Affiliate/redirect | Phishing risk |
|---|---|---|---|---|
| drughubportal.live | Every 48 hours | Each verification cycle | None | Screened |
| Dread forum thread (official) | PGP-signed by team | On rotation only | None | Low (with key check) |
| Ad-supported link directories | Rarely | Irregular, often stale | Common | High |
| Clearnet search results | Never | Not applicable | Common | Very high |
The official Dread thread is the primary source — this directory monitors it and republishes verified addresses with timestamps. Using this directory is not a shortcut around Dread; it is a pre-checked snapshot of Dread's verified output, with the three-step verification already completed for you.
| Property | Primary link | Mirror link |
|---|---|---|
| Onion address | drughub75…ad.onion | rughubrwg…id.onion |
| Marketplace content | Identical | Identical |
| Account access | Same account on both | Same account on both |
| Order visibility | Full order history | Full order history |
| Response time | ~9 sec (Tor avg) | ~12 sec (Tor avg) |
| DDoS priority | Primary target | Secondary (lower traffic) |
before you connect
Getting the correct drughub market link is necessary. Using it safely is a separate step. These nine practices cover the technical baseline. None of them require advanced knowledge — only consistent habits.
Copy it, paste it into Tor Browser, check the footer fingerprint. That is the complete process. The access manual covers everything else.
This website is an independent informational resource. We do not distribute marketplace links to visitors arriving through direct access.
Verified .onion addresses are displayed exclusively to visitors arriving through search engine results. Find this page through Bing or Google for DrugHub market links.